1 min read
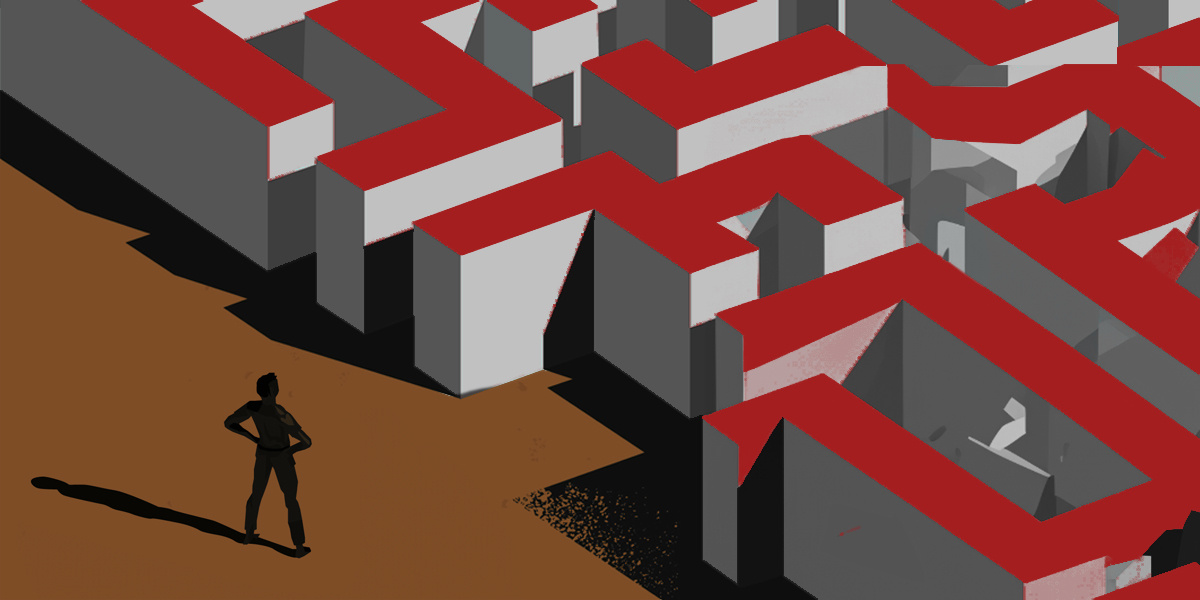
Navigating the Cybersecurity Maze: Carving Your Path in a Multifaceted Domain
In the vast and ever-changing cybersecurity landscape, there is a place for every kind of talent. By focusing on your chosen track, you'll not only...
2 min read
![]() IronGate
Jan 9, 2024 6:41:55 PM
IronGate
Jan 9, 2024 6:41:55 PM

In today’s era of complex digital threats, managed service providers (MSPs) are tasked with more than just managing IT infrastructure and services; they must also be proficient in addressing cybersecurity incidents. Clients depend on their MSPs not only for technological support to drive their businesses but also for expertise in cybersecurity. In the event of a security breach, these clients turn to their MSPs to act quickly to restore operations and reduce business downtime. This places MSPs in a critical role. They are expected to supply hardware, recover systems, and manage incident response protocols. The depth of trust in the MSP-client relationship underscores the necessity for MSPs to understand and apply effective incident response procedures to protect both their clients and their own operations.
In a cyber incident, immediate and effective containment is crucial. MSPs should have a well-defined containment plan that includes steps like isolating affected systems by disconnecting network cables, isolating network segments from the internet, or disconnecting internet access entirely. A rapid response helps limit the damage by preventing the spread of the incident, whether it's a malware infection, a ransomware attack, or unauthorized access.
In the event of a ransomware attack or other malware infection, MSPs should avoid restarting or powering down systems. Rebooting affected systems can exacerbate the situation, potentially leading to further corruption or preventing the operating system from booting up. Knowing the nuances of system handling during an incident is critical to preserving evidence and maintaining system integrity for further investigation.
Pure-play MSPs should establish relationships with specialized incident response partners. Before an incident occurs, these partners need to have predefined roles and responsibilities. Collaboration ensures the incident response team can seamlessly take over from the MSP with minimal downtime or learning curve. Essentially, the MSP initiates the incident response, and the IR team continues the efforts without disruption, ensuring a streamlined and effective response to the incident.
MSPs must develop and maintain comprehensive recovery plans. These plans should include provisions to set up new systems for critical applications quickly, enabling the swift resumption of business operations. While new systems are being set up, the infected ones should remain online but isolated, under the supervision of the IR team until they can be safely released for rebuilding. This strategy ensures business continuity while still addressing the cybersecurity incident thoroughly.
For MSPs, mastering incident response procedures is not just about technical prowess; it's about being a reliable, trusted partner in today’s threat landscape. By having a solid containment strategy, understanding the nuances of system management during an incident, collaborating effectively with IR partners, and having robust recovery plans, MSPs can significantly enhance their value proposition to their clients, ensuring both operational continuity and cybersecurity resilience.
Contact us today to learn more about our Digital Forensics and Incident Response (DFIR) services.

|
Steve Ramey has spent the past two decades helping clients protect, investigate, and respond to events involving their digital interests. He has led hundreds of data breach investigations, assessed incident response and security programs, and successfully advised organizations through extortion negotiations. |
1 min read
In the vast and ever-changing cybersecurity landscape, there is a place for every kind of talent. By focusing on your chosen track, you'll not only...

1 min read
October 24, 2023 IronGate CEO Steve Ramey a Featured Speaker at The QA Financial E-commerce Forum in New York

1 min read
October 24, 2023 IronGate CEO Steve Ramey on PLUS Podcast Series, Season 2, Episode 1